Why Cybersecurity Often Misses the Mark
Most organisations don’t ignore security – they struggle to keep up with it.
Assessments happen once a year. Reports land in inboxes. Tools generate alerts. But without context, prioritisation, and follow up, real risks stay unresolved.
Security becomes reactive, fragmented, and difficult to govern.

New Services Are Deployed
Software Ages
Configurations Drift
Security Is Not a One Off Exercise
Your external exposure changes constantly.
New services are deployed. Software ages. Configurations drift. Threats evolve. What was secure six months ago may not be secure today.
Without continuous visibility, organisations are always looking backwards.
What We Mean by Continuous Monitoring
Rather than a single point in time assessment, we provide ongoing visibility into what’s exposed to the outside world. We focus on your external attack surface; the services, systems, and configurations attackers can actually see and probe. This turns security from an abstract concept into something measurable and manageable.
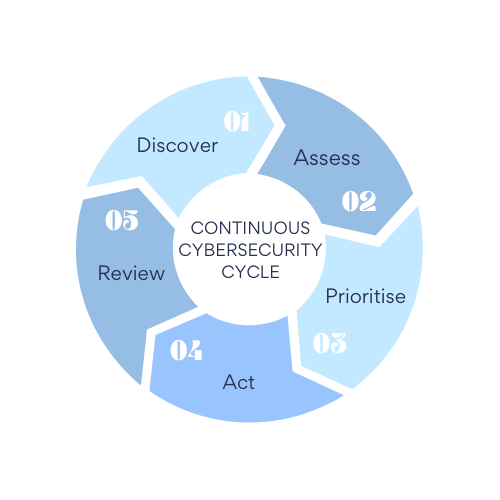
- 01. Discover: Identify what is externally visible across your attack surface.
- 02. Assess: Analyse exposures, vulnerabilities and misconfigurations in context.
- 03. Prioritise: Focus on what presents real risk — not just what generates alerts.
- 04. Act: Address issues through remediation, configuration or patching.
- 05. Review: Track changes over time and confirm security posture is improving.
How Blue Sky Approaches Cybersecurity
Our approach is deliberately practical.
We combine automated external scanning with experienced oversight, translating technical findings into meaningful risk insight aligned with Cyber Essentials and ISO 27001 expectations.
There’s no sales theatre, no panic language, and no unnecessary tooling. Just honest visibility and steady improvement.
Because good security should reduce stress — not create more of it.